Windows is, according to just about any security expert you ask, the operating system most vulnerable to attack. Unless the security expert happens to be from Microsoft, that is. So it was quite refreshing to see Microsoft admitting to a spike in attacks on Windows this week.
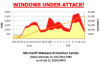
According to a posting by Holly Stewart on the Microsoft Malware Protection Center Threat Research & Response Blog Windows XP and Windows 2003 are officially under attack. Russia has seen ten times as many attack attempts than the global average, and the UK has witnessed a "surge" in the words of Microsoft.
Referring to the vulnerability that was patched by a Microsoft critical update and described in Security Bulletin MS10-042 which can allow remote code execution through the Windows Help and Support Center, Stewart states "As of midnight on July 12 (GMT), over 25,000 distinct computers in over 100 countries/regions have reported this attack attempt at least one time". The spike in attack attempts over this last weekend was really quite dramatic, and comes after Microsoft announced the timetable for releasing the fix.
Stewart says "these attack attempts have continued to expand and some new attack patterns have come into play" adding that the attacks witnessed in the wild "work only on Windows XP" and not Windows 2003. Of course, that hasn't stopped people from trying to exploit the vulnerability on versions of Windows that are not susceptible to it. Indeed, Microsoft says it has noticed that the most recent attacks have been indiscriminate when it comes to OS version rather than targeting XP as with the earlier attempts.
Despite some reports suggesting that Apple is more insecure than Microsoft in terms of vulnerabilities the truth will always out, and it's nice to see Microsoft coming clean on this. What would also be nice, and we've said it here at DaniWeb on more than one occasion, would be if people simply stopped using Windows XP which is becoming something of a zombie amongst operating systems .
Interestingly, this is the same vulnerability that was made public by a Google security researcher less than four days after he discovered it. "Public disclosure of the details of this vulnerability and how to exploit it, without giving us time to resolve the issue for our potentially affected customers" Mike Reavey, Director of the Microsoft Security Response Center says "makes broad attacks more likely and puts customers at risk". Reavey, and Microsoft, insist that the software vendor is in the best position to understand and repair such problems as it is the vendor who wrote the code in the first place. Which is why Microsoft is an advocate of what it calls responsible disclosure.
Microsoft asks that any security researcher who thinks they have found a vulnerability that is not resolved by the " 10 Immutable Laws of Security " to contact them at [email]secure@microsoft.com[/email] with the following information:
Type of issue (buffer overflow, SQL injection, cross-site scripting, etc.)
Product and version that contains the bug
Service packs, security updates, or other updates for the product you have installed
Any special configuration required to reproduce the issue
Step-by-step instructions to reproduce the issue on a fresh install
Proof-of-concept or exploit code
Impact of the issue, including how an attacker could exploit the issue